HOW TO HACK SOMEONE GMAIL
It is rightly said by Albert Einstein,
“It has become appallingly obvious that our technology has exceeded our humanity.”
Introduction :
Technology today has revolutionized our times in all possible ways. There is no time when we work without a modern gadget in our hands from dawn to dusk. Be it a global Hire A Hacker plague of mobile phones or our fingers stuck on computers,i-pads, tabs, modem gadgets are such an integral part of our everyday life today that we can’t imagine a world without them.
This modern technology has also brought a lot of problems related to how to operate them and how to use various tools. With these problems, many solutions have also arisen with a bundle of alternatives. Whether using Ms Excel, various calligraphy, removing bugs, detecting plagiarism, or hacker for hire someone’s Gmail for any security purposes, solutions are provided in very easy formats. These are never-ending solutions, procedures, and explanations.
Now we will discuss the procedure of hacking someone Gmail:
This is a bullet point that hacking an email is a very easy task if you have the credentials and passwords and the user has lost the passwords. It is also considered an important and convenient way to test the account security of your mobile and the operating device.
There are some methods and several ways you can use for this process, i.e., hacking someone’s Gmail.
1. Understand the full formation process and working of Gmail:
You should have all the essential knowledge about the procedure as well as the working of Gmail before hacking someone’s Gmail. It is an incredibly secure as well as safe service provided to the users, and they are highly reliable and have the trust of the customers. So the only way by which you can hack someone’s Gmail is through stealing their passwords or by knowing their password from secondary sources. It should be noted that if the person of whom you are stealing the login credentials or hacking Gmail is having two way authentication, then you will necessarily require their mole device as well and there is no alternative of this two-factor authentication.
2. Legal knowledge :
You should understand legal formalities and regulations before starting any hacking, as it can be illegal and may lead you to prison because it is illegal in most of the area to seize or access or hack someone’s email without prior permission or authorization of the email holder.
3. Using a key logger :
As the name itself suggests key logger is a tool or an instrument that logs the keystrokes of the device on which it is installed. There are a lot of options available free on online websites. These popular options include Actual Key logger, spyrix free key logger, black box express, kid logger, net bull, and many more. These are some of the options of key loggers available that can be used for hacking someone’s email.
The process of using it is as under:
Get administrator access on the targeted computer. It is to be noticed that on many computers, passwords will be admin or just completely blank. Installing the key logger on the targeted computer without the permission of the owner of the target computer is considered illegal. Start the service so that it begins recording the keystrokes of the computer. And this is how you will be able to Hire a hacker someone’s email. You need to be on the computer so that you can check the strokes of the key logger of the targeted computer . .
View the key loggers:
There are many ways of getting the logs. Some key loggers will send the stroked keys on your email however some require you to explore them yourself on the program running. It means some are provided to you on email however others are collated live when the host computer starts. It should be focused that if the person of whom you are stealing the login credentials or hacking Gmail is having two way authentication then you will necessarily require their mole device as well and there is no alternative of this two factor authentication.
4. Use the browser’s password manager :
This process includes various process which can be followed with the given steps:
a. Open the web browser that your target uses on their computer .
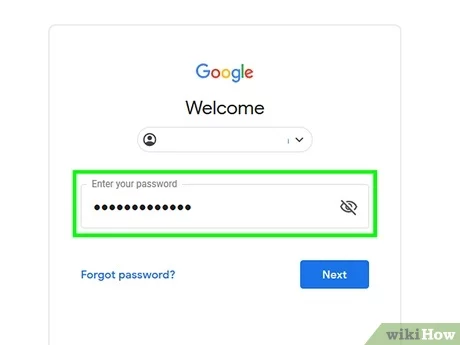
b. Open the password manager which can be done by various browsers like internet explorer , chrome , firefox or safari. You can set these, change the password, replace the password, and save some other password. This will provide you with dominant control over the targeted computer.
c. Find the password for your target’s Google account.
d. Display the password
e. Rite down the password and then close the password manager.
f. Make sure to try the password from some other computer or device.
These are some of the ways which can be used for hacking someone’s Gmail. There is also one different way by using a packet sniffer, but it needs a detailed knowledge of this process as well as downloading and installing the Wireshark app. This is considered as one of the detailed processes of hacking someone’s email though it is tough and detailed but it is highly secured and certified.
Conclusion :
These were some of the processes and ways that can be used for hacking someone’s email . it needs to be kept in notice that you should have prior permission from the person whose Gmail account is hacked by you otherwise it is considered as illegal.
Modern gadgets and technology seem to have helped to connect us virtually, but in reality, they have forced us to lead an isolated life.
In today’s time, a life without modern gadgets will be one of human emotions and feelings and not of robotic expressions and methods . We will be able to build relationships and not increase the friends list. In fact the statement “gadgets are excellent slaves, but dangerous masters” aptly defines their importance in our lives.



