Which attacks does DMARC not protect you from?
While DMARC protects you from a wide range of cyberattacks, it is no silver bullet. There are tactics that cybercriminals can deploy to evade detection and bypass authentication checks. It is important to understand what they are and what you can do to prevent them. Using additional technologies along with DMARC will only strengthen the security of your domain and take it to the next level.
A Brief Introduction to DMARC
DMARC serves as an email verification protocol that prohibits malicious emails that attempt to impersonate individuals and businesses. It works to protect your organization’s emails in close association with Sender Policy Framework – SPF and Domain Keys Identified Mail – DKIM.
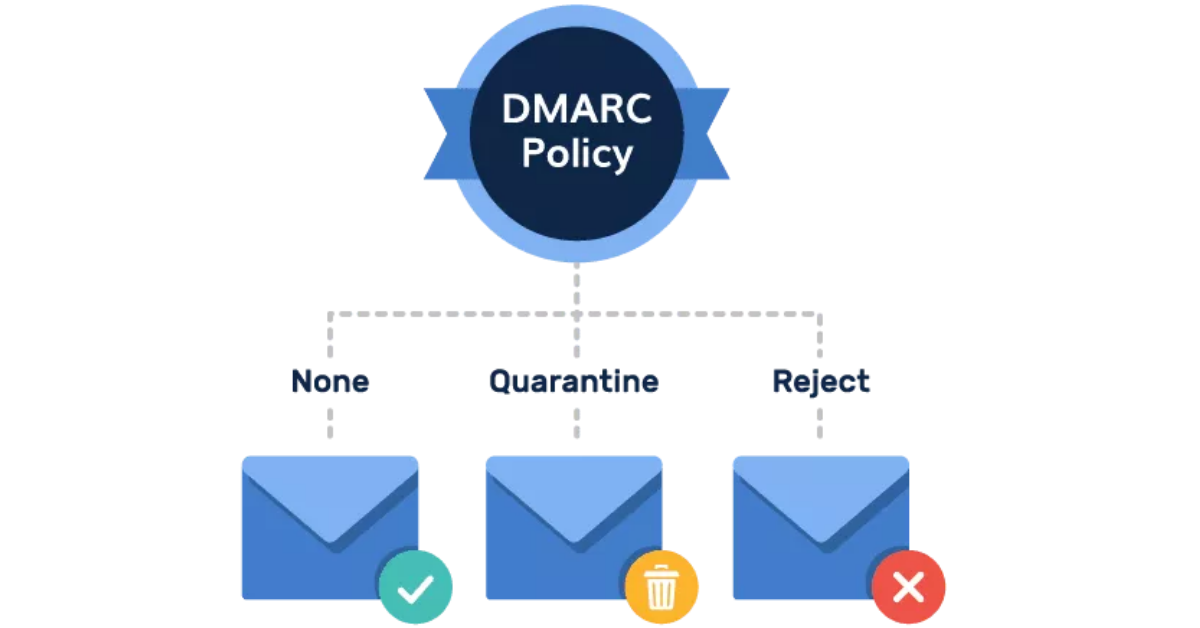
Organizations use DMARC to defend against BEC, spoofing, and phishing attacks. It is used as a mitigating control to prevent such attacks, protecting emails being sent and received by your organization. By using it, your organization takes control of what happens to messages that fail authentication tests – should such emails be rejected, quarantined, or delivered?
The Need for DMARC
DMARC serves as a proposed standard that allows the senders and receivers of emails to coordinate and share information about the emails being sent to each other. It helps combat malicious email practices which can put your organization at risk.
When conducting any business-related operations, email is the primary means of communication with customers, employees, and stakeholders. Messages that have not been secured are easier to spoof, and hackers find new and innovative ways to use various email scams.
DMARC is used to help secure the emails being sent and received by your organization to reduce the number of phishing, spoofing, and spam practices. This allows senders to improve email authentication infrastructure and ensure that the emails sent from their domain are authenticated.
Which attacks does DMARC not protect you from?
Even though DMARC has evolved as one of the leading standards for email authentication and verification, there are still some attacks that DMARC cannot protect your organization from. They are as follows:
● DMARC cannot protect against phishing attacks from lookalike domains or Indirect Impersonation
When enabling DMARC, you must list down all the domains that your organization owns. All the enlisted domains are then DMARC protected, and hackers will not be able to send phishing emails using those domains. However, the hackers can use domains that resemble your domain name very closely, and DMARC cannot prevent this.
For example,
If the domain for your organization looks like “organization.com” and you implement DMARC protection on that domain, hackers can still use “organizations.com” or “organizationadmin.com”.
To prevent this, it is a recommended practice that all such domains are bought by your organization and parked. Then you can set a DMARC policy for parked domains to stop attackers from using them for malicious purposes. This will prevent the hackers from using such domains to send phishing emails to your customers or your employees.
● Hackers can use External Domains to attempt phishing attacks
There exists a high percentage of business dealings that comes from external sources. Since the other organizations your business is dealing with are unlikely to have authentication standards in place, your employees remain vulnerable to impersonation from external sources.
● Domain Name Abuse
While Domain name abuse can also include trademark infringement—for example, if you register a domain that infringes on another company’s trademark, here it refers to domains that are used for phishing, malware, botnets, or other activities that are generally recognized as illegal or at least harmful.
However, the term domain abuse is also used to describe a number of other types of “bad” domain registrations. This includes cybersquatting or registering a domain that is confusingly similar to an existing trademark, as well as registering a malicious typo of a popular website’s name. Another type of abuse is registering a large number of domains with the goal of reselling them to unsuspecting buyers later on.
If you believe that your domain registration has been affected by this type of domain abuse, you can contact your domain registrar to report it.
● A hacker may gain physical access to the IT assets of your organization
DMARC standards, even if implemented properly, cannot replace a firewall. While a firewall monitors the data exchanged between the computers in your organization and the internet to detect malware, DMARC monitors the mails that are being sent or received against the domains that have been registered. Thus, if a hacker gains physical access to the IT assets in your organization, DMARC authentication will not be helpful.
● Man-in-the-Inbox attacks
Lastly, DMARC cannot protect your organization or employees from phishing attacks or malicious emails if the hacker has gained access to the user’s mailbox. Since the mail is coming from a legitimate account, SPF and DKIM for the mail check out, and the mail seems authentic.
Key Takeaways
Setting up DMARC standards for your organization is just beginning to protect your organization against possible phishing attacks. It is vital to grasp the functionalities as well as limitations of DMARC to better your defenses against cyber threats. Even though DMARC doesn’t prevent all types of attacks that may affect your organization, it serves as an effective tool to block out all spoofed emails, improve brand image and increase deliverability.
DMARC technology when complimented with an antivirus and a firewall can form the basis of a well-rounded and impenetrable email security posture at your organization.
Part of PowerDMARC’s effort is to ensure that every domain used by your organization is protected with DMARC to help your organization prevent phishing attempts and help secure your mail. Our customized dashboards allow businesses to analyze and maintain their DMARC policies, SPF, and DKIM and monitor DMARC reports.



